Photo FOMO: Sad camera stats, a free studio, and a splash photography tool
VSCO Open Studio, Oakland, Calif. VSCO Afraid of missing out on the latest photo industry news while you’re out, well, actually taking pictures? Photo FOMO is all the news you might have missed this week, published on the weekends. Alongside the biggest stories of the week, like the Olympus PEN E-PL9, Apple ProRes Raw, Premiere Pro’s A.I.-powered color matching, Lightroom’s new camera profiles and Gnarbox 2.0, find briefs on the latest in accessories and photo industry news from this week with Photo FOMO. VSCO’s new open studio in Oakland is totally free to use Real estate in the Oakland, California area is expensive — but mobile photo editing company VSCO is launching a space that photographers can use for free. The VSCO Open Studio is available for non-commercial projects, allowing photographers to reserve a four-hour slot in the space. The space, located inside VSCO headquarters, has a mounted seamless background and also includes gear to borrow. VSCO says the studio helps support the company’s mission to equip creators with the tools they need. VSCO had a similar studio in New York but closed the space when the New York offices closed last year. At the time, the company said it was planning to reopen the studio at the company headquarters — and now that day is here. Camera sales are dropping — again Camera sales finally showed signs of stabilizing in 2017 after years of decline but the latest Camera and Imaging Products Association numbers show early 2018 sales aren’t as promising. Sales for all cameras in January were about 70 percent of the sales during the same time last year, with February slightly better at about 73 percent of last year’s numbers. Eliminate the compact point and shoots and those numbers are less depressing — with 80 percent in January and 94 percent of the 2017 sales for the first two months of the year in interchangeable lens cameras only. In February, camera sales for fixed lens cameras were nearly half of the number sold the previous year at 55 percent. MIOPS latest trigger is just for splash photography MIOPS A single drop of water can create a visual photo subject — and camera remote company MIOPS is making it easier to control everything from the size of that water droplet to when it falls. The MIOPS Splash is a water drop kit photographers can control with a smartphone. The Splash controls the water droplet while also triggering the camera or a flash. Using the app, photographers can control the size and timing of a single drop or two subsequent drops of water. The MIOPS Splash retails for $79, with the mount adding another $20. Google’s computer vision is probably better than you are at classifying bowls of ramen Computer vision can recognize faces and label objects but one researcher recently created a program that can tell just from a photo which restaurant a dish of ramen came from. Using Googles AutoML Vision, Kenji Doi, a data scientist, decided to see how well the artificial intelligence could recognize different bowls of ramen. After just a day of training, the computer was able to guess correctly 95 percent of the time which location of a Tokoyo-based chain ramen restaurant came from. Doi suggests the software distinguishes on the chains different locations by looking at topping placement and the meat on top. Free stock photo platform Unsplash now has an iOS app Unspalsh is known for its selection of free stock images and now those images are easier to browse from an iPhone or iPad. This week, Unsplash launched an iOS app. Unlike the platform’s earlier apps for wallpapers and for Apple TV, the new iOS Unsplash app allows users to browse and download stock images from the platform, including a drag-and-drop download option. Photographers could win a free photo trip with the #CaptureDedication contest Photo software Capture One is hosting a free photo contest on Instagram and the grand prize winner gains a photo workshop trip. The grand prize in the #CaptureDedication contest is a trip to either Shanghai or California with photographer Paul Reiffer. During the trip, the photographer will also have access both Reiffer’s expertise and Phase One XF gear. The winner will also get a Capture One Pro license. The second place prize is a Wacom MobileStudio Pro 16 and Capture One Pro software, while the third prize is a Wacom Intuos Pro and the software. To enter, photographers simply need to share an image on Instagram with the hashtag #CaptureDedication with an explanation of why the image is special and how it shows your dedication. Winners will also need to follow @Captureonepro on Instagram. The contest closes at the end of the day April 23. Spark now supports square videos Square aspect ratios just fit better inside that social media scroll, so Adobe Spark Video is enabling the 1:1 aspect ratio. Adobe cited a recent study suggesting square videos see around 30 percent more views and between an 80 and 100 percent increase in engagement. The new aspect ratio is under the resize option inside Spark Video. Editors’ Recommendations https://www.digitaltrends.com/photography/photo-fomo-april-6-2018/









 against the attackers. Security effectiveness starts with closing the obvious gaps and making security a business priority,” Martino comments in the statement.
against the attackers. Security effectiveness starts with closing the obvious gaps and making security a business priority,” Martino comments in the statement.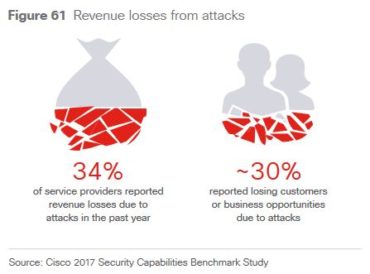 “As criminals continue to increase the sophistication and intensity of attacks, businesses across industries are challenged to keep up with even foundational cybersecurity requirements,” the statement notes.
“As criminals continue to increase the sophistication and intensity of attacks, businesses across industries are challenged to keep up with even foundational cybersecurity requirements,” the statement notes.